Speaker 1: 00:01 On this episode of Edge of the Web.
Arlie Hartman: 00:04 It’s an old statement, but it’s still true today. If you don’t know what the product is, you’re the product. If you’re using a service, and you’re not paying for it, just understand that they’ve got to monetize it. Once again, making a smart risk decision, is it fair, do I want to communicate with my friends and family and share pictures and do all the things, then I need to have a Facebook and then understand the data that I put in there or the activities that I do while I have Facebook app installed on my phone or on my computer while I do these other activities, that that’s going to feed back into the machine.
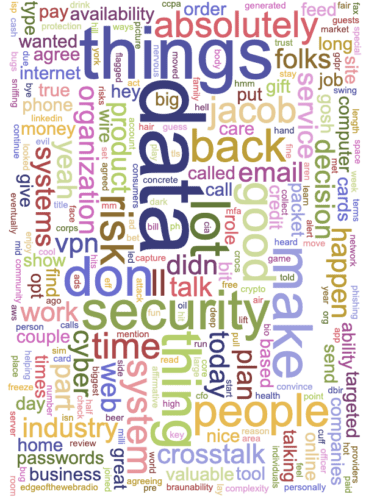
Speaker 1: 00:35 Your weekly digital marketing trends with industry trend setting guests. You’re listening and watching Edge of the Web. Winners of Best Podcast from the Content Marketing Institute for 2017. Hear and see more at edgeofthewebradio.com. Now, here’s your host, Erin Sparks.
Erin Sparks: 00:57 Oh my, what’s that? [crosstalk 00:00:59]
Arlie Hartman: 00:59 We talked about everything being a risk calculation, so this is an example of poor risk management. There’s a game called Beersbee that we play every summer as a competition together as friends. I made the poor decision of wearing… I packed very quickly to go for this weekend out with friends in the woods, you can see there it’s in the woods, and for some reason, I didn’t pack any socks or shoes. I had my pair of sandals and then I had a pair of Crocs.
The key to this game, you need to understand is you have to hold a drink in your hand while you throw a frisbee. This may or may not contain beer. I didn’t want to soak my nice sandals with beer because it tends to spill when you’re very active in this game. Unfortunately, I choose the Crocs on wet concrete and it was not a great decision, as you can see in this picture. The alcohol there is probably about six foot up out of the cup as I’m quickly going to the concrete as I slipped.
Erin Sparks: 01:57 But did you save the drink? That’s the important thing.
Arlie Hartman: 02:00 I’ll say most of it landed on me.
Erin Sparks: 02:04 Just wring it out, it’ll be fine.
Arlie Hartman: 02:07 That is a great example of poor risk management. I did not consider the risk when I stepped onto the concrete in those Crocs.
Erin Sparks: 02:15 I was not part of that particular insert there. I just want you to know is that that’s all Jacob’s idea.
Arlie Hartman: 02:20 You’ll notice it was a photo credited to Jacob Man Photography at the bottom of that.
Erin Sparks: 02:24 The watermark there. Well, let’s introduce our guest to our audience. Arlie’s been an IT Security Specialist, a Senior Security Officer, a Security Operations Manager, Head of Information Assurance, Cloud Information Security Officer and is currently a Chief Information Security Officer and Director of Information Security at BraunAbility. Okay, we get it. You know security. You just wanted to have that in the title so many times.
Arlie Hartman: 02:52 I’m hoping that eventually through osmosis, you’ll get more secure.
Erin Sparks: 02:58 If there’s our optimization for this podcast. Just transcribe that, we’re going to be locked in. That’s your professional bio history, but give us a history, really the backstory of how you got to be in security and what led you to the role at BraunAbility?
Arlie Hartman: 03:16 Sure. I got out of high school, didn’t really know what I wanted to do, did a couple jobs here and there, and decided I wanted to move out to the mid-west. I grew up here in northern Indiana, moved to the mid-west and we’re doing more of the same jobs that just got me from here to there, paycheck to paycheck, trying to figure out what I wanted to do, and I joined the service while I was in Seattle. Joined the Marine Corps, I was in the Marine Corps for three and a half years.
Erin Sparks: 03:46 Thank you for your service.
Arlie Hartman: 03:47 That’s not why I said it, I just explained it, but you’re very welcome.
Erin Sparks: 03:50 Appreciate it, man.
Arlie Hartman: 03:51 A lot of my service was just cleaning a lot of things.
Erin Sparks: 03:55 You weren’t serving in the protection mode, you were protecting the mode.
Arlie Hartman: 04:00 Exactly. You got it, yes. It was a lot of just-
Erin Sparks: 04:04 The [inaudible 00:04:04]
Arlie Hartman: 04:05 … trying to teach people how to use systems and the like. I did that but every Marine’s a rifleman, so you learn a lot about how to engage the enemy, how to make sure things are fortified and secure in the physical kinetic space more than cyber. But I picked up a little bit of IT on the way. I got out, came back to Indianapolis, was in book publishing for a while, in computer books, and that’s how I got my interests kicked off, carrying over from the military into that, and then started working for a couple IT shops here in town, got my associate’s degree and then transitioned fully into IT.
I joined a local hospital system here in town called Saint Vincent Health, which is part of a larger organization called Ascension Health. That job really, there is no body. I was doing quality assurance if you will, which was really the complaints department. Anytime IT screwed something up, they’d send me up there to get yelled at.
Erin Sparks: 05:02 The sacrificial lamb.
Arlie Hartman: 05:03 Right, they were like, “You guy, you got yelled at professionally for three years in the Marine Corps, this should be cake.” I was like, “Yeah, absolutely.” Until I met nurses. Brutal. But transitioned out of that and moved into security because nobody else wanted to do it and that’s where I found what I was really good at and what I really loved. I like tearing things apart and figuring out how they work and really having the curiosity of the way systems and people and processes work and organizations are built. Then just being able to constantly have a career that challenges me to continue to keep up and learn as I go. That’s what I love about security.
Over the years I’ve moved into different areas, I’ve done compliance, I’ve done security, I’ve done cyber security, I’ve done information assurance. All of these are words that really just mean managing the risk, systems risk or information risk for an organization and then working with folks with IT systems to make sure they understand the domain that they’re in and hazards that they face.
They always aren’t very apparent, not only to the IT folks, but also the business folks. I act a lot of times as a translator too. That’s what I enjoy about cyber security and that’s the path that got me there. I’ve always enjoyed it. I’ve seen a lot of different things over the years.
Erin Sparks: 06:20 I bet you have.
Arlie Hartman: 06:23 It’s always a fun time. I would say probably the worst job I’ve ever had in cyber security was before we had web filters, as you might see as traditional today. I was a human WebFilter, so a lot of times I had to watch. When we saw something flagged or something odd, I would have to then go in the logs and find out everywhere you went online and the go there myself and see the same things that you saw. I’ve seen some pretty horrible things. That’s when I began to appreciate Bourbon. I will say that.
Erin Sparks: 06:54 Oddly enough, the Marion County Public Library hired our firm a couple times to actually analyze the public monitors, all the machines, for 24 different branches of their library.
Arlie Hartman: 07:09 Wow. I bet that’s an interesting thing.
Erin Sparks: 07:11 Oh my gosh. You talk about some scary stuff. We didn’t have to go look at the same stuff.
Arlie Hartman: 07:16 I get it.
Erin Sparks: 07:17 But the categories of what people were searching for, and we just won’t broach most of them are on this show. We don’t want to get ourselves flagged.
Arlie Hartman: 07:24 Exactly.
Erin Sparks: 07:25 But at the core of it, what’s the riskiest component in cyber security? A loaded question.
Arlie Hartman: 07:33 That is a very loaded question. At the end of the day, there are only so many ways that systems can be tricked into doing things. We talked about the confused up issue earlier. Probably one of the ones is that there are risks companies face on the availability of their systems and things that they can do. Whatever their mission is, whether it’s providing a service to customers, it’s producing a good like we do at BraunAbility, we produce vans for the disabled. One of my concerns are we want to make sure that those lines are always available to continue making a product. That’s called system availability.
Security has what’s called the triad. I’ll make this as simple as I can. There’s confidentiality, there’s integrity and availability. What that really means is confidentiality, we’re going to maintain this as a secret thing, there is integrity, we’re going to make sure that its the same data, two plus two is always equal to four. Then availability, that you can always find that number four I’ve written down somewhere. I’m going to keep maybe that four a secret, but then I also want to make sure its available to those who need to be able to see it and that two plus two is always four. But they move-
Erin Sparks: 08:41 They pull against each other.
Arlie Hartman: 08:42 They pull against each other. It’s a delicate balance you have to work with. I always want the system to be available, so I can’t patch it as much as I’d like to. So the available of the integrity goes down and the confidentiality goes down. Maybe that’s okay because it’s a system that doesn’t have sensitive data on it. It needs to be available, it needs to have some integrity, the confidentiality can go way down, so maybe we don’t put controls on there, we’re inspecting data and things like that.
You have to do it. Or if you have a machine that takes orders in from a customer where they type in their social security number and their banking information and things like that, guess what? That availability gets to go down and a lot of the confidentiality and integrity goes way up. You have to balance that. There are risks to availability which I worry about, the ransomwares, the malwares, system availability DDoS, this is when systems aren’t available due to web traffic. There’s also the confidentiality.
I think one of the biggest ones that are really coming up right now is there are a lot of problems today with… I was just looking at the Verizon’s Data Breach Investigations Report, DBIR, comes out every year, it’s been going out for 11 years, so it trends over time and it’s really an aggregate report from a lot of different providers, Verizon’s the Marquee sponsor. But they go to a lot of different vendors that respond to incidents all over.
Erin Sparks: 09:57 It’s a coffee table book in your house, right?
Arlie Hartman: 09:58 Yeah, it’s a good size report, about 60 pages. It’s broken up by industry which is nice. You’re able to look at healthcare, manufacturing, retail, a little different attacks they face and the paths the attacker took obviously. Webmail and email are very good, pretty prevalent ways to get malware into a company. Pre-texting, calling before hand to say, “Hey, we’re offering a special on insect eradication.” Okay great, maybe send that a couple times, send a fax, call in a couple times, and then you show up in your little bug gear and you’ve got your backpack on and you say, “I’m here to spray the data center, here’s my work order signed by Bill.”
That person’s already gotten like, “I’ve gotten five emails and I’ve gotten a phone call about this, I bet my boss did too, so this is probably legit. Go ahead and go to the data center and spray it.” Then you walk in and you get access to everything. That’s an example of pre-texting. Trying to enforce the idea that you should be there or you should be allowed to do something.
There are, like I said, several different risks, business email compromise is another one that’s a way for you and I to talk and then Jacob and I to talk and then eventually I convince Jacob that I’m you and that I authorize the ability for him to pay one of our vendors who by the way is my bank account, and he’ll wire the money off and then come back to you and go, “Hey, I took care of that thing you wanted me to.” And you’re like, “What thing are you talking about?”
Erin Sparks: 11:19 So you’ve already isolated [crosstalk 00:11:21] a risk in our system.
Jacob: 11:22 … I just needed Walmart gift cards with you.
Arlie Hartman: 11:25 So Walmart-
Erin Sparks: 11:26 I think he’s already paid you, Jacob, as a risk in the system here.
Arlie Hartman: 11:32 I’ve had a filter set up on our email system before at a company where I say any time that I see an email going out that has a gift card anywhere in the body and has an attachment, I immediately want that stopped and flagged so we can see if they’ve scratched off $3000 worth of gift cards. Now, you ask me, why would you do such a thing? It was because we had an executive admin work for a CFO, and she got an email from the CFO saying, “Hey, I’m putting together gifts for everybody but I can only pay for them with gift cards. You know I’m extremely busy. If you could go out and just get me $3000 worth of gift cards and scratch them all off and take a picture of them and email them to me, I can get it paid for.”
Erin Sparks: 12:14 Come on.
Arlie Hartman: 12:15 And she did it, absolutely. These things happen.
Erin Sparks: 12:21 What you’re doing is really establishing the true risk in the system and that’s us. Right?
Arlie Hartman: 12:27 Right, absolutely right.
Erin Sparks: 12:29 Let’s circle back around to ourselves. How do we secure ourselves first? What’s the best place to hide a log in for my computer? Under my keyboard?
Arlie Hartman: 12:39 Some people would argue under your keyboard’s safer than on the internet.
Erin Sparks: 12:43 This goes back to war games, back in the day, right?
Arlie Hartman: 12:46 Exactly. It depends on do I trust my presence on the internet more than I trust the locks on my house? I don’t know, maybe. It depends on if you have smart locks and they’re connected to the internet. That’s a whole other thing.
Erin Sparks: 12:56 It’s full circle. Isn’t it?
Arlie Hartman: 12:57 Yeah, exactly.
Erin Sparks: 12:59 We’re all going to be locked into our house by Skynet, you realize that?
Arlie Hartman: 13:02 The risk is you have to make that risk decision. If you have to write down five different passwords and put them under your keyboard, verses using the same username and password for five different sites, go ahead and use your keyboard. At the end of it, there’s been several things that people have debated since the end of time, complexity over length of password. I prefer length every time over complexity. Nest would agree. I would rather you make sure you don’t use the same password everywhere. If you need a password tool, like LastPass or RoboForm or something that has the ability to help you create unique passwords and store them each time, you should probably use that.
Erin Sparks: 13:40 You probably have to remember the password for that password tool, right?
Arlie Hartman: 13:43 You do, you do. You want to make sure that that’s one you definitely have long and can remember and let it select all the random ones for you. Now, the trick there is always, always, always protect your whatever it is with multifactor authentication anytime you can. Some people would say, “Oh, if I get a text message, there’s a way for me to do a chip swap, I can take your SIM, convince somebody to give me that SIM and then I get your codes that you’re presenting to get in.”
Erin Sparks: 14:08 Sure.
Arlie Hartman: 14:09 Yeah, but that’s still better than username and password. It’s a risk based decision.
Erin Sparks: 14:13 It’s a heck of a lot more difficult to do that and you just-
Arlie Hartman: 14:16 Than it is to guess your Fito 123 right on your password.
Erin Sparks: 14:19 Check this out. We just did a search on the top 10 most common password, still in 2019, 123456, 789, qwerty. Password, 111111. ABC123. Password one. What the hell?
Arlie Hartman: 14:34 True story.
Erin Sparks: 14:34 Are these 2019.
Jacob: 14:34 I’ve got so many I got to change now. A question online here from Mike. He says, “What about Apple’s password generator?”
Arlie Hartman: 14:46 I don’t know. First of all, I won’t endorse anything just on air. I’ve never looked at it, I couldn’t tell you. I’m always suspicious of any sight that I go to that wants me to test my password by me just typing a password into some rando’s website. That makes me a little nervous. You can have those passwords generated but you wonder what kind of cookie tracking is going on between website to website to see where you went with that generated password. Things like that would make me take pause.
I’ve not seen every password manager out there but there are several good ones and typically they are pretty reputable especially if they’ve worked with the open source community or had any review done or audits done.
Erin Sparks: 15:26 Apple does have a function now where it’s actually creating or generating a password for you, so does WordPress for that matter. WordPress now has… it provides you a strong password right out of WordPress. There’s a number of these tools out there. But even that, you’ve got to look at what’s behind the scenes that’s generating it for you when it gets down to it. Unless you’re testing the tool emphatically. Then you always have to have a little bit of concern.
Arlie Hartman: 15:58 It’s the whole caveat emptor. You’ve got to understand what you’re agreeing to and what you’re trying to do.
Erin Sparks: 16:03 What about passphrases?
Arlie Hartman: 16:04 Passphrases are good. That’s where I talked about that length over complexity, that I definitely would prefer a passphrase every time. If you can come up with a 15 character passphrase that you can remember and don’t continue to use it over and over again. That’s where I put it on that password manager, that 15 character passphrase and then allow it to just do pseudo generated random gibberish that are 15 to 20 characters long for each one of your other passwords. All the better.
Erin Sparks: 16:27 All right, so first, get your own house in order, right?
Arlie Hartman: 16:30 Right.
Erin Sparks: 16:31 Second is knowing how you’re connecting to the internet. We’re talking cyber, obviously in this space, what about VPN’s? What kind of VPN’s… Would you recommend a VPN, first and foremost, for your connectivity?
Arlie Hartman: 16:45 There are a couple different arguments there. A lot of the web today is TLS and it has that little lock on it that’s the SSL/TLS connectivity between you, your endpoint and the web service encrypted. Now, a lot can still be gleaned from that traffic. You can still determine that Jacob went to Facebook. I can’t tell you exactly what he typed into the password field, but there are ways that I could trick you then. The VPN just adds another layer of encapsulation so that way I can’t exactly tell where you’re going. But the rub there is understanding who you’re signing a contract with in order to get that VPN. There’s been speculation that the majority of the VPN providers are actually shell companies for intelligence agencies to collect data about you. Whether or not you trust the CIA verses America Online, I don’t know. It’s depending on what you want to do with your ISP. Personally, I run a VPN server in AWS. I control the logs on it, I can get the [crosstalk 00:17:42]-
Erin Sparks: 17:41 Are you part of the CIA?
Arlie Hartman: 17:43 No, I am not.
Erin Sparks: 17:43 Okay.
Arlie Hartman: 17:44 Nor have I ever been part of the intelligence community.
Jacob: 17:45 Wait a minute, if you were-
Erin Sparks: 17:47 If you were, were you allowed to say?
Jacob: 17:50 If you were part of the CIA, what would you have to say right there?
Erin Sparks: 17:54 Are you legally obligated to acknowledge that?
Arlie Hartman: 17:56 I don’t think you are.
Erin Sparks: 17:59 Exactly. That’s the second response. We know now.
Arlie Hartman: 18:02 I think it’s a good idea to obfuscate your traffic. Just understand, once again, just like your password manager you have to pick out, you have to be a little bit worried about the VPN service provider or roll your own.
Erin Sparks: 18:17 Okay, I’ll dig it. For those playing at home that don’t know what a VPN is, back up real quick. Go ahead and describe what that is, what the functionality is.
Arlie Hartman: 18:26 VPN stands for virtual private network and what it allows you to do is create a tunnel, if you will, over the normal every day internet that’s a direct connection between your computer and another server and then that server will then proxy your connection to websites, wherever you’re going online, the dark web, whatever you may want to go to.
Erin Sparks: 18:47 He looked at Jacob as soon as we’re talking dark web there. All right, nice. I’m getting a pretty good profile of you now Jake, thanks.
Arlie Hartman: 18:56 Typically you’ll see ads for them online, $5.99 a year, $10 a year, $2 a month, whatever it may be. I’ve heard of Nord and a few others that are out there. Like I said, just got to do your research, see the reviews, see if anyone has offered any audit or any promise to their users. This is a big thing, so the other part of that is as a consumer, understand what you’re signing away. I know it’s very tough to read those terms and conditions, especially from iTunes that you agree to every time there’s an update and things like that.
Erin Sparks: 19:26 Sure.
Arlie Hartman: 19:28 As much as I would love to say it’s on the provider to make clear their intentions of what they’re going to do with your data and what they’re going to do, it’s also on us as consumers to do our homework too, to look at what they’re doing with our data and what they’re saying are part of the terms of services that you’re agreeing to.
Erin Sparks: 19:46 Okay. All right. You pulled me out. I was going to, I was going to pull this around at the end of the show, but let’s talk about that right now because this is a very very hot topic and out of the 2016 election, we had a lot of fake news, we had a lot of reports of manipulation. Well, we’re at 2019 and there are bills going up on Congress to be able to get big data to reveal the value of this privacy data that they have. That right there, what would be your takeaway? You don’t have to commit, but what are your thoughts about government regulation on data that’s collected by these large entities that are in it for material gain, for advertising and in capital capital endeavors. Right?
Arlie Hartman: 20:34 Right.
Erin Sparks: 20:34 What do you think about that?
Arlie Hartman: 20:37 The only statements of… it’s an old statement but it’s still true today, if you don’t know what the product is, you’re the product. If you’re using a service and you’re not paying for it, just understand that you’ve got to monetize it. Okay. Once again, making a smart risk decision, is it fair? Do I want to communicate with my friends and family and share pictures and do all the things? Then I need to have a Facebook and then understand the data that I put in there or the activities that I do while I have Facebook app installed on my phone or on my computer while I do these other activities, that that’s going to feed back into the machine.
But flip side is I think it… as long as it forces companies to be very transparent with what they’re doing with your data and what data they collect on you, and then you have the right to be forgotten and you have the right to understand everyone they’ve shared that data with and that those people will honor the same agreement that you’ve made with the company with that data, which is like the premise of GDPR and CCPA, and the GDPR is more of the European data protection and CCPA is like a California flavor that they’re trying to do or they are doing, I shouldn’t say trying, they are doing.
Erin Sparks: 21:44 But that one thing is adopted across the country?
Arlie Hartman: 21:47 Not yet. No. We still don’t have a universal cyber regulation. We don’t have a universal breach notification yet. All 50 states have different types of breach notification rules on how long it can be before you’re told that your data’s been compromised. There’s no standard saying you have to do these things in security. They are for health care or for credit card data, but nothing forever. NYD effaces New York standard for financial institutions that are based in New York or do business in New York.
There are all different rules and regulations. But I don’t know whether or not I would support a particular one over another one. I’ve worked with in them all, I’ve worked with in different schemes, whether they were regulatory for healthcare and finance and on a credit cards, all different rules. Sometimes they make things easier. Sometimes they make things harder with anything. Poorly written regulations are worse than no regulation.
Erin Sparks: 22:46 But you’re talking standards, certain standard definition to keep everybody on the same playing field. But from a forcing of entities to be able to reveal that type of data, what’s your sentiment on that?
Arlie Hartman: 23:05 I just want them to… that’s my major concern, is I want to understand what data companies have about me. I want to understand who they’ve all shared it with, what they’re doing with it and some assurance that the people that they’re sharing it with will do the same thing that they’ve promised to do with the data. If you’re using it for x, Y, and Z, let me know that and I can either opt in or opt out, but you need to tell me that and it needs to be in plain English. It needs to be a way that I can consume it.
Then I need to be forgotten. If I want to opt out, I want to collect all the data, take it with me and then opt out of the program. These are things that I think generally are good. I believe there was just a report that went out two months ago that saying the most valuable commodity is now data. It’s not oil anymore. You can get more money for data than you can for oil. It’s only going to get more and more so I think we just need to take a pause and set some ground rules for like, this is what I know about myself and what you know about me and what you’re doing about it with that.
Erin Sparks: 24:06 So if big data’s actually forced to reveal this content all of a sudden, it’ll be on that consumer to make that decision and consumers are by their very nature, Lazy.
Arlie Hartman: 24:24 That’s true.
Erin Sparks: 24:25 Honestly that’s part of the entire Cybersecurity. That’s what keeps you in business.
Arlie Hartman: 24:30 No one’s ever bought a product because it was secure.
Erin Sparks: 24:33 But at that point in time, could there very well be a cobble industry of helping consumers even translate the type of data that’s being used on a consumer’s behalf? Is it?
Arlie Hartman: 24:43 I don’t know, maybe. That’s an interesting topic. I have not really thought about an advocate if [crosstalk 00:24:48] It would have to be something like the Electronic Frontier Foundation, EFF, which is an organization near and dear to my heart that I’ve always supported EFF.org. If you get a chance to go out, that would be my only pitch. But it has to be there’s some foundation or known for profit or some state sponsored entity that would have to do that. Just much like when there was the affordable care act and there were navigators, I think we created. I don’t know if there’s a data steward or data navigator out there that could help folks, that could go to as a resource to be like, “Hey, I don’t understand this. I don’t know.”
Erin Sparks: 25:24 You can imagine if they are actually pushed to reveal all this content about you, you’re not going to be able to sift through it. It’s going to need tomes of information and you… that’s as scary as not seeing the data, is they’re trying to figure out, okay, where is all this supposed to be going? By and large, if people can’t spend the time to even read the terms and conditions on a particular data platform and they’ll just go to the bottom and hit accept, then they’re in it for-
Arlie Hartman: 25:56 Whatever they’ve agreed to.
Erin Sparks: 25:57 … whatever they agreed to. That’s what’s tougher because we’re right now on the front here of this next economy. You’re absolutely right, is that you are going to be more valuable and your behavior’s going to be more valuable than ever before. You either can commit and agree to just go ahead and-
Arlie Hartman: 26:16 Participate in an [crosstalk 00:26:17]
Erin Sparks: 26:17 … paper me with every advertisement you can, or can find yourself where you can possibly, and I’m just waxing optimistically, that we may find an area of almost like a DMZ or something where, okay, you can have this much data but this is my core private data that I don’t want to be exploited. Almost a commerce on my side.
Arlie Hartman: 26:40 I want to opt in so much on this product and here’s what I’ll trade. Right?
Erin Sparks: 26:43 Right.
Arlie Hartman: 26:44 I think that that’s an interesting way to look at it. I don’t want to paint marketers as bad people. They’re trying to provide a valuable service [crosstalk 00:26:53] which is-
Erin Sparks: 26:53 We’re all evil, you know that.
Arlie Hartman: 26:55 But you want to offer me a targeted ad, which is going to be much better than an ad that’s not targeted [crosstalk 00:27:00]-
Erin Sparks: 27:00 Absolutely.
Arlie Hartman: 27:00 … because I could care less about a hair product obviously. I would much rather see about beard products and hair products and vice versa.
Erin Sparks: 27:09 By the way I’ve got some really cool beard oil in the-
Arlie Hartman: 27:12 Really?
Erin Sparks: 27:12 Yeah, I got to share that with you. Absolutely.
Arlie Hartman: 27:15 Absolutely. These are the things that if I got to watch some streaming channel entertainment and I didn’t get to have to watch the same stupid five commercials that was selected because based on whatever reason, that’s not obviously targeted towards me, I would much rather watch 10 different commercials than to get that streaming service that would be, maybe two of those would be actually super targeted at me. That would be valuable to give me a product I didn’t know about.
Erin Sparks: 27:37 It’s almost like that. Now the consumer could very well be empowered with their data as-
Arlie Hartman: 27:42 That could make it easy. Versus me trying to go through some self-selected of telling you all the things on my interest that you could just tell. There could be some valuable there. The threat to democracy on the other hand though, is a little more terrifying to me and these platforms being leveraged for campaigns and thought influence, and things like that are a little more of the frightening Orwellian thing that I think really needs to be clear and transparent, not only to regulators but the individuals and citizens themselves.
Erin Sparks: 28:08 Psychology tests and experiments that are being actually done on set of platforms. We’ll actually name them because we’re streaming on one. That is very frightening because now you’re in the manipulation of, we’ve been in the headline Clickbait society for a very long time where we’re no longer are people actually investigating and taking it upon themselves to understand stories and concepts, but they’re being led astray by that headline. Not even clicking on it, just that it’s showing up in the feed. Now you have organizations that can manipulate that and be able to adjust your mood and attitude and belief system by that feed. We’re farther down the rabbit hole than we thought we were.
Arlie Hartman: 28:53 Absolutely. Well, today the way that a lot of countries are so polarized right between two different parties, typically it only takes a 2%, right?
Erin Sparks: 28:53 Yeah.
Arlie Hartman: 29:04 You wonder like, oh, these mass influence campaigns. They didn’t do it. Well, they didn’t have to swing 51%.
Erin Sparks: 29:09 Not, it was a nudge.
Arlie Hartman: 29:10 They had to swing 2% or one and a half percent, just a little to one direction and that’s enough [crosstalk 00:29:16]
Erin Sparks: 29:16 Or even just convince people not to vote.
Arlie Hartman: 29:18 Right. [crosstalk 00:29:19]
Erin Sparks: 29:20 It’s the same bloody thing. All right. Well as the pressing is that is, I would like to us-
Arlie Hartman: 29:25 Talk about threat to western democracy and everything we cherish.
Erin Sparks: 29:28 I had dropped the mic. But let’s swing back around. So I’m sure it was some buzz words that the audience has heard in news reports and maybe around the office so we’re all on the same page, packet sniffing, what is that?
Arlie Hartman: 29:42 The way that we move data back and forth on the plumbing, i.e all the wiring and-
Erin Sparks: 29:46 All the inner tubes?
Arlie Hartman: 29:47 On the inner tubes, right. We do that with packets, so packet switching is a way that those things happen from here to there. Packet sniffing is the ability to capture all those, we call it pcap, Packet Capture. We often say pcap or it didn’t happen. I believe that the kids today say, picture didn’t happen maybe, but we call it pcaps or it didn’t happen, so it’s just I can do a packet sniff on your machine and watch everything you did everywhere you went, milli second by milli second by doing a packet capture or packet sniffing.
Erin Sparks: 30:13 You can actually do that inside of a closed network?
Arlie Hartman: 30:15 Yes.
Erin Sparks: 30:17 By this type of [crosstalk 00:30:19]
Arlie Hartman: 30:19 Inserting yourself as what’s called a man-in-the-middle-attack and that’s the ability for between your between your asset and that. That’s when I talk about those VPN providers. They’re technically being a man-in-the-middle that you’re allowing and opting into. That they could snip all your traffic. Because you’re terminating your encryption at them and then going on elsewhere.
Erin Sparks: 30:37 Oh, my Lord. Oh gosh. Okay, phishing with a ph not an f-
Arlie Hartman: 30:42 I’m going fishing next week by the way.
Erin Sparks: 30:44 Oh, nice. But ph is not where we want to go, so what’s the fishing realm?
Arlie Hartman: 30:49 That’s anytime that you get an email and click on the link or open an attachment or do something that an attacker is trying to get you to do by sending you an email to get you to do it, right?
Erin Sparks: 30:49 Mm-hmm (affirmative).
Arlie Hartman: 31:00 There’s phishing, there’s wailing, where you go after executives, spear phishing, where you go after targeted individuals. If you’re on Linkedin and I find out there these people are system engineers at this company, I’m going to attack them and their family members trying to get into their home network, so that way I can work my way back to the company.
Erin Sparks: 31:16 Exactly. Just thinking about that is that you’re revealing your title and your organization status, in that organization and by the very definition you’re saying, “Okay, here I am for attack, manipulate me.”
Arlie Hartman: 31:26 Mm-hmm (affirmative).
Erin Sparks: 31:27 Oh my gosh. Well, Cryptolocker and ransomware, what do you talk about them?
Arlie Hartman: 31:31 This all are under the umbrella of digital extortion. I’m either taking away your systems or your data and interfering with your mission. Whether that’s to make money or to serve the poor or whatever it is. Then you have to pay me ransom to get that data back or key to that encryption if it’s ransomware or CryptoLocker.
Erin Sparks: 31:52 Got It. So we can make realm whenever extortion comes through, now they’re looking for some Bitcoin, right?
Arlie Hartman: 31:58 Mm-hmm (affirmative).
Erin Sparks: 32:00 Give us an idea of what Bitcoin is or cryptocurrency is for the folks at home.
Arlie Hartman: 32:05 Now that could be a whole episode in itself. You have an expert in the other room on cryptocurrency, but as far as I understand it, it’s just the way… at the end of day, all these things are away from me to get money anonymously to me on the internet that’s untraceable. Wire fraud, you can usually typically get the wire back from the different banks. If I’m trying to get money deposit into account, then I’ve got to pay somebody a mule to pick that money up and then wire it to me. Crypto is nice because crypto is good anywhere on the internet instantaneously. That cryptocurrency is just an agreed ledger between individuals where they value something under a certain dollar amount. They then exchange that information back and forth between each other in their wallets. That is the poorest example of cryptocurrency I’ve ever given but that’s it off the cuff.
Jacob: 32:49 Well, it’s good. I think the big thing is it’s not reversible.
Arlie Hartman: 32:52 Yes, exactly.
Jacob: 32:54 Once you send Bitcoin to somebody, the only way to ever get it back is to have them agree to send it back to you.
Erin Sparks: 32:58 Correct. That’s a good point Jacob. And it was used to be able to deregionalize currency and be able to have a currency 2.0 where it’s a global market as opposed to a regional market. But should we blame cryptocurrency on the existence of ransomware?
Arlie Hartman: 33:16 That’s the same as reason we would blame the existence of cartels based on cash. It’s just a medium that they work at.
Erin Sparks: 33:24 Roger that. Well, if somebody find themselves needing Bitcoin, suddenly it just so happens, how do you go about doing that with any level of protection? Are these malware and these extortion platforms that good that once it’s there, you’ve got to pay up and I hate-
Arlie Hartman: 33:43 An ounce of prevention is worth a pound of cure. What this means is have a plan, an incident response plan and exercise it, knowing what you’re going to do when it hits. Making sure that you have good quality backups and you’ve put the thought process into your business continuity and disaster planning so that way you don’t have to fall victim to this extortion. There are many different types of extortion, not just the crypto mining. I’ve gotten a few phone calls here or there and there. There was a phone call from an executive who’s told me he’s received an email about some compromising photos taken from his laptop and I was like-
Erin Sparks: 34:18 Always makes you wonder why they’re nervous.
Arlie Hartman: 34:20 Right, I was like, don’t worry it said this, that and the other, right? And he was like, “Yeah, and they had a password.” I was like, “Well that’s not the password you use on the site.” “No, but it’s the password I use on another site.” And I’m like, “Yeah, that’s called credential spraying or credential packing.” Anytime you see these lists of these common passwords or there’s a dump, then they’re going to go out and spray it across an organization trying to see if they can get lucky with that.
Erin Sparks: 34:40 All right. You said something just then, you got to skip past it. It almost like you’re in that assumption role, but the assumption role is that it will happen?
Arlie Hartman: 34:51 Right.
Erin Sparks: 34:52 Absolutely. Not if, but it will.
Arlie Hartman: 34:54 It will happen.
Erin Sparks: 34:55 Planning for the breach. Personally as well as for corporation, the personnel play a role in the organization, a very high degree of risk as well. What do you recommend putting a plan in place personally as well as corporately a for an organization, what should they start looking at? That’s a big question I realize that, but where’s the first points of review that they should be looking at?
Arlie Hartman: 35:26 Sure. I think you just look at those top hits. Like, Hey, if somebody were to send an email to someone in our organization, what would be the worst thing that could happen? You start to look at, well these folks have roles too in order to send cash outside the organization. Now we need to make sure that they understand what they should be doing. The other side of it is, what is your instance response? I keep harping on this, but understanding that you’re having a plan for a disaster and exercising that plan. Just like we’re always been told at home, you need to have a plan for escape during a fire. What do you do during a tornado? In the work, unfortunately we’ve started going through active shooter drills or things that we have to have right in place.
Cyber is no different. It’s the same as the kinetic domain. What will we do when we have these things go wrong? You need to have that plan and exercise that plan. That’s the biggest thing. I do want to mention one other thing and I forgot to mention earlier for personnel and people. We talked about MFA and having a password tool and the ability not to use the same password across different accounts. Lastly, in light of all of these situations where a lot of social security and other information has gotten out, freeze your credit. It is a service that is offered free of charge on the three large credit monitoring companies. Freeze your credit with all three of them. It is a little bit inconvenient because you have to do, then unlock it if you want to do anything that requires your credit check. But it is probably the easiest thing you can do and the most effective to keep people from stealing your identity for purpose of opening accounts.
Erin Sparks: 36:52 That’s interesting. These platforms all have these tools and there’s that one that’s better than the other, but you need to know what’s happening. Any of these credit monitoring platforms also have a good alert system, should have a good alert system of what’s happening and if you’re getting trolled, or I should say not troll, if you’re to getting exploited any of these hacks could very well reveal your data. What do you do whenever you come across your username or password on the dark web? It’s great to be able to know that information and like, “What the hell do I do with this?”
Arlie Hartman: 37:28 Right. You just need to make sure that you think about that account and try to remember, have I used that password anywhere. That’s where you got to me and we start going, what are the most valuable websites to me? I’m going to change the password right now for them. Hopefully I’m going to make a unique password for each one. That way when I do get, one of them does get popped, I know the exposure because I only have one password and it’s only for that one site.
Erin Sparks: 37:47 My gosh. We use password monitoring programs here in our office and there’s so many passwords, and remembering whether or not that was the same or not, you really had to do that internal audit. Go from stem to stern and see how… It probably is very, very humbling to see how similar your passwords were. Just for ease of views.
Arlie Hartman: 38:11 Absolutely.
Erin Sparks: 38:12 Oh my God, it’s serious. Okay. Well, what have we skipped over in this show, what we failed to mention?
Arlie Hartman: 38:18 I can’t really think of anything, we’ve covered a lot between data privacy and security and risk management and understanding what you need to do, so not. I think that’s it.
Erin Sparks: 38:28 That’s all right. All right, well we’ve got to ask you because we always ask of our guests. What were the bugs you about your industry right now? Not that you know Jacob Man.
Arlie Hartman: 38:38 I guess the big thing is, there’s a general feeling of apathy. A lot of folks feel like there’s nothing we can do. We’re always going to be a hacked. Where I talked about biggest thing is response, having those things. There are things that you can do. You can make smart choices, you can do the right thing, just adding additional layers to help protect yourself. What bugs me the most is the apathy of it and our industry is very… what’s the word I’m looking for here? There’s a lot of marketers and vendors in our space right now, and I’m hoping that they can take the time to learn what our true challenges are versus what the Buzzword Bingo is in the way that they market to us.
I took this role five weeks ago with chief, and every day I look at Linkedin there’s another 400 people who’ve looked at my profile with either sales person or marketer on their title. It gets to be a bit of a feeding frenzy at a time where you just don’t answer email or phone calls anymore.
Erin Sparks: 39:33 Oh My gosh. All right. Well, hey if we weren’t apathetic, you’d be out of a job though-
Arlie Hartman: 39:38 Good point.
Erin Sparks: 39:39 It’s all job security, right?
Arlie Hartman: 39:42 It is job security. There’s a time that you eventually you get tired of rolling that rock up the hill.
Erin Sparks: 39:46 Any fun facts, anything? Let me ask you this, what do you enjoy about your industry, just to wrap it up?
Arlie Hartman: 39:52 Sure. What I really enjoy about the industry is a lot of folks in it are like me. They’re very curious and there’s no particular gender, color, orientation or anything about our industry and that’s the great thing about it is, really it could be somebody as old as me or as young as coming right out of school. They’ve got that drive and an interest and they’re always willing to share information. We’ve got a very vibrant community of people who like to share and come and do shows and things like this.
Erin Sparks: 40:20 Absolutely.
Arlie Hartman: 40:20 It’s always a great opportunity to just to get back.
Erin Sparks: 40:22 No, we certainly appreciate your time today and as a wealth of information, we wish you all the best of luck and championing in this issue. Because we need more knowledge that’s dispensated to the lay person like ourselves.
Arlie Hartman: 40:22 Absolutely.
Erin Sparks: 40:37 So, thank you so much for participating today. Anything we can promote for you?
Arlie Hartman: 40:40 Yeah, a couple of things. One would be the Electronic Frontier Foundation, EFF.org is a great organization that is looking out for consumer and individual citizens rights around the world and helping you stay surveillance free.
Erin Sparks: 40:54 Very good. All right, final last words for somebody who’s scared to death of what we just heard today.
Arlie Hartman: 41:01 Don’t be scared. This is a risk based decision. You can’t get afraid of flying just because everyone publicizes how many airplanes there are. You need to make the right decision and understand what you’re agreeing to and you’ll be fine.
Erin Sparks: 41:14 Read the fine print.
Arlie Hartman: 41:16 That’s what it comes down to.
Erin Sparks: 41:17 That’s what it’s there for.
Arlie Hartman: 41:18 Absolutely.
Erin Sparks: 41:18 All right. Well, thank you so much Arlie. I appreciate all the information and we’re certainly going to lift you up from afar. We want to make sure you follow Arlie on Twitter Arlie, @arliehartman, as well as on over on Linkedin, Arlie Hartman. Thank you so much for joining us in studio today. I really appreciate it.
Arlie Hartman: 41:34 Absolutely was my pleasure. Thank you.
Erin Sparks: 41:36 Thanks for listening to Edge of the Web Radio. A special thank you to all of our colleagues over at Site Strategics for helping us produce this show each and every week. Special thank you to Arlie Hartman in the studio. You might want to make sure you check out all the videos and audio and all the stories we have over edgeofthewebradio.com. That’s edgeofthewebradio.tom. We’re going to be talking to Bill Slawski this next show, so you better stay tuned. We’re going to be talking to one of the deep deep deep knowledge, gandalfs of SEO. How about that? There’s a moniker form.
Hey, be sure to like, rate and review this show. We certainly appreciate all the feedback and that’s what helps us optimize our own site content. Let us know how we’re doing and we’ll certainly keep on giving you as best as we can these nuggets of gold from the world of Edge of the Web Radio. Thank you so much and we’ll talk to you next week. Do not be a piece of cyber driftwood. Bye bye.
